Your network operations center receives an alert at 3 AM: unusual call volume from Nigeria routing through a European interconnect. The CLI is properly formatted, call durations average 90 seconds, and the traffic profile matches a known enterprise customer’s campaign. Do you block it and risk angering a paying client? Or let it through and […]
Some fraud doesn’t steal identities, it builds them. A few real details mixed with fake ones create a person who doesn’t exist but looks completely legitimate. That’s synthetic identity fraud: convincing, calculated, and built to slip through routine checks. Unlike traditional identity theft, synthetic identities leave no one to sound the alarm. They slip into […]
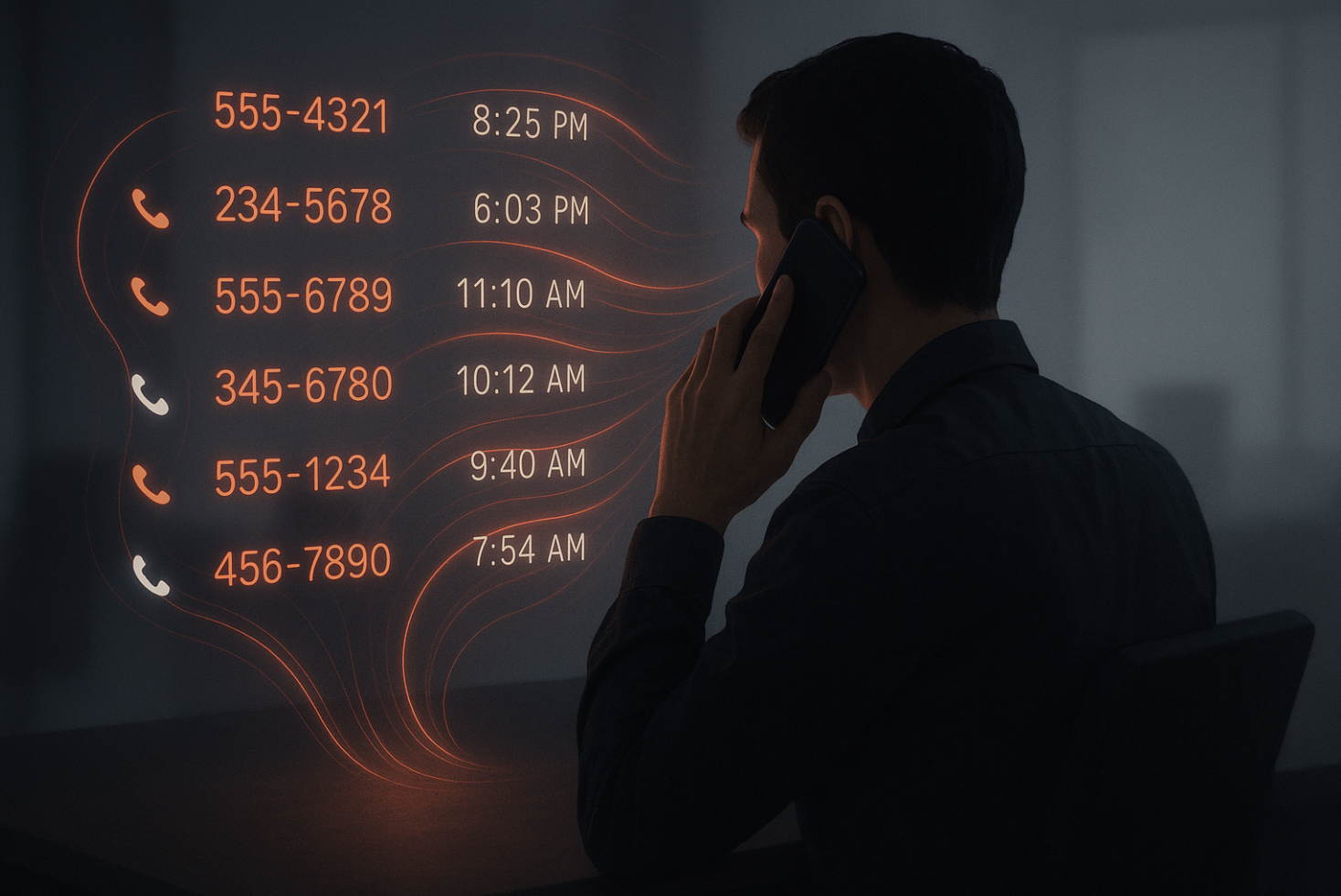
When most people think about phone security, they picture eavesdroppers listening in or hackers trying to intercept the actual content of a call. But the real risk often isn’t in what you say, it’s in the invisible trail you leave behind. That trail is called metadata, and it records far more than people realize. Every […]
Why Location Alone Can No Longer Be Your Security Strategy You’ve probably heard the advice: “Don’t answer calls from unknown numbers.” But here’s the twist—what if that number looks like it’s from your own country, or a place you’ve always associated with credibility? Your instinct changes. You pick up. And that, right there, is the […]
Why Header Data Doesn’t Tell the Whole Story Let’s pull back the curtain on something that looks simple—but isn’t. Attestation labels (A, B, C) from the STIR/SHAKEN framework may offer a quick snapshot of a call’s trust level, but they don’t guarantee full authentication. These tags can be spoofed, allowing fraudulent calls to slip through […]
There’s growth and then there’s a surge. In telecom, that difference matters more than ever. What used to be a steady climb in voice traffic has turned into an all-out flood, driven by AI bots, global call centers, hybrid workforces, and expanding cross-border telecom traffic. And while many networks are built to scale, few are […]