Fraud Prevention & Telecom Security
Expert insights and real-time strategies for telecom fraud prevention—covering threat analysis, SIM boxing, CLI spoofing, Wangiri, IRSF, and the multi-layered defenses stopping fraud before it ever connects to your network or subscribers.
Picture this: a wire transfer request comes in over a voice call. It sounds exactly like your CEO—the breathing, the pauses, the “ums” between sentences. You approve it. Later, you find out your CEO never made that call. This is not a hypothetical. This is generative AI telecom fraud in 2026, and it is already […]
Some fraud doesn’t steal identities, it builds them. A few real details mixed with fake ones create a person who doesn’t exist but looks completely legitimate. That’s synthetic identity fraud: convincing, calculated, and built to slip through routine checks. Unlike traditional identity theft, synthetic identities leave no one to sound the alarm. They slip into […]
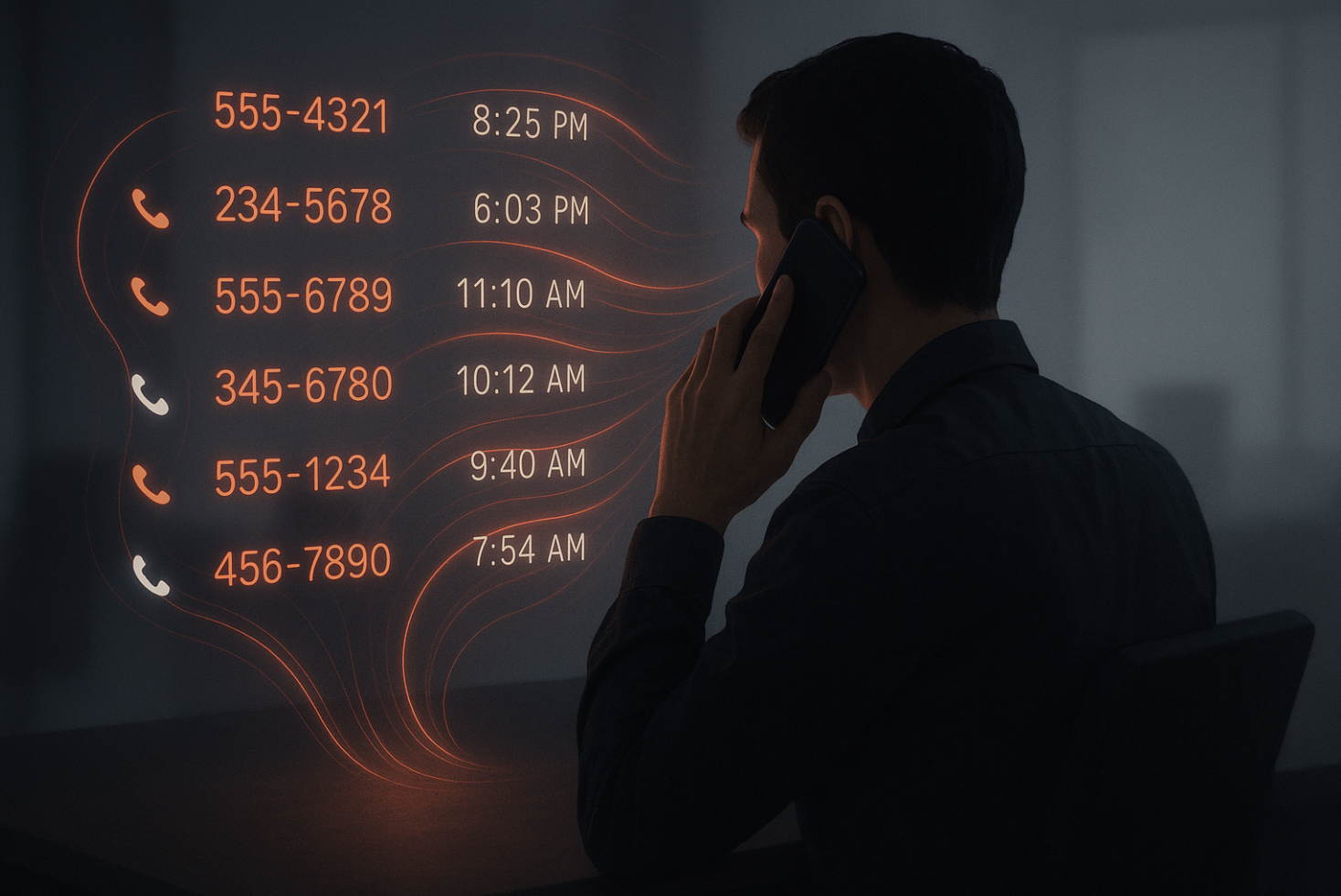
When most people think about phone security, they picture eavesdroppers listening in or hackers trying to intercept the actual content of a call. But the real risk often isn’t in what you say, it’s in the invisible trail you leave behind. That trail is called metadata, and it records far more than people realize. Every […]
Why Location Alone Can No Longer Be Your Security Strategy You’ve probably heard the advice: “Don’t answer calls from unknown numbers.” But here’s the twist—what if that number looks like it’s from your own country, or a place you’ve always associated with credibility? Your instinct changes. You pick up. And that, right there, is the […]

You’re placing a legitimate international call. It’s part of your daily operations—maybe you’re trying to reach a customer, partner, or vendor but the call never gets through. It either goes straight to voicemail or is ignored altogether. Later, you find out it was marked as “Spam Likely.” Sound familiar? This isn’t just frustrating—it’s bad for […]
Multi-carrier routing is everywhere in the telecom industry. It helps companies save on costs, improve call quality, and keep their networks reliable. But it also brings some hidden headaches—especially when it comes to tracking call data and catching fraud. For telecom companies, ignoring these challenges can lead to revenue losses and missed fraud activity. What […]