Telecom Infrastructure & Modernization
Navigating telecom network modernization across TDM, SS7, IP, and 5G environments—exploring how carriers can protect and upgrade their infrastructure without leaving legacy systems exposed during the often lengthy and capital-intensive transition to modern networks.

Some fraud doesn’t steal identities, it builds them. A few real details mixed with fake ones create a person who doesn’t exist but looks completely legitimate. That’s synthetic identity fraud: convincing, calculated, and built to slip through routine checks. Unlike traditional identity theft, synthetic identities leave no one to sound the alarm. They slip into […]
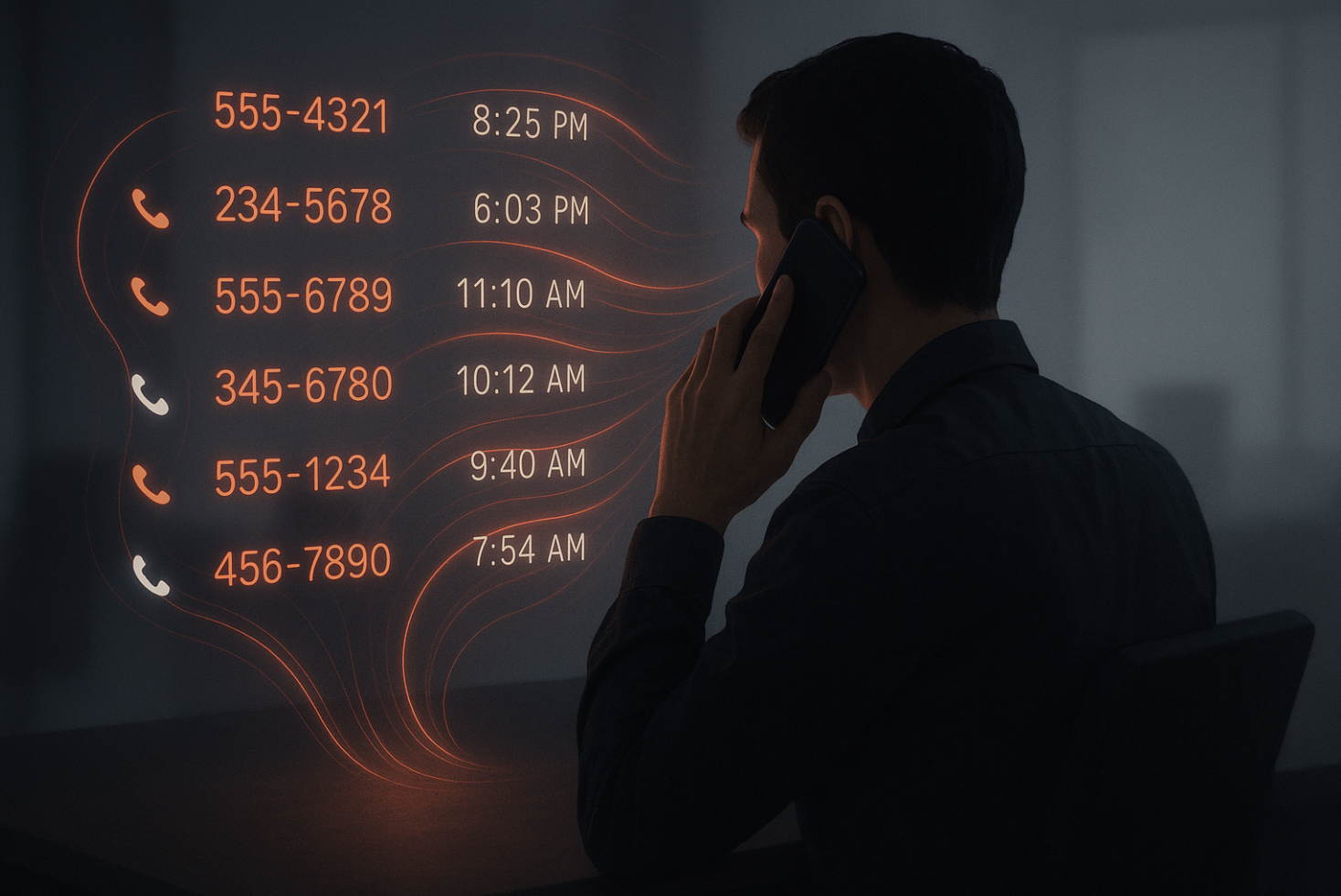
When most people think about phone security, they picture eavesdroppers listening in or hackers trying to intercept the actual content of a call. But the real risk often isn’t in what you say, it’s in the invisible trail you leave behind. That trail is called metadata, and it records far more than people realize. Every […]
Why Location Alone Can No Longer Be Your Security Strategy You’ve probably heard the advice: “Don’t answer calls from unknown numbers.” But here’s the twist—what if that number looks like it’s from your own country, or a place you’ve always associated with credibility? Your instinct changes. You pick up. And that, right there, is the […]
Let’s break down some common weak points in call validation and explore practical ways to address them. Along the way, we’ll also touch on how tools like 1Route are stepping in to help providers close these gaps. Let’s break down some common weak points in call validation and explore practical ways to address them. Along […]
Picture this: A telecom provider reaching out to update a customer on a service upgrade or alert them about a potential service disruption. The phone rings, but it’s flagged as spam and ignored. That customer misses out on vital information, and the telecom company misses an opportunity to serve and retain a loyal customer. This […]
As the holiday season approaches, the demand on industries intensifies, and telecommunications is no exception. Whether it’s companies handling more customer inquiries, families making long-distance calls, or shoppers seeking support, call volumes surge dramatically in the final quarter of the year. This influx of activity brings both opportunity and risk for telecom providers, making accurate […]
- 1
- 2




