Picture this: a wire transfer request comes in over a voice call. It sounds exactly like your CEO—the breathing, the pauses, the “ums” between sentences. You approve it. Later, you find out your CEO never made that call. This is not a hypothetical. This is generative AI telecom fraud in 2026, and it is already […]
It is 2:17 a.m. in the network operations center. Two alarms are live. A legacy TDM interconnect is degrading on one screen while an IP trunk holds steady on another. Fraud flags are spiking at the boundary between them, and nobody wants to be the engineer who called the cutover too early. This is the […]
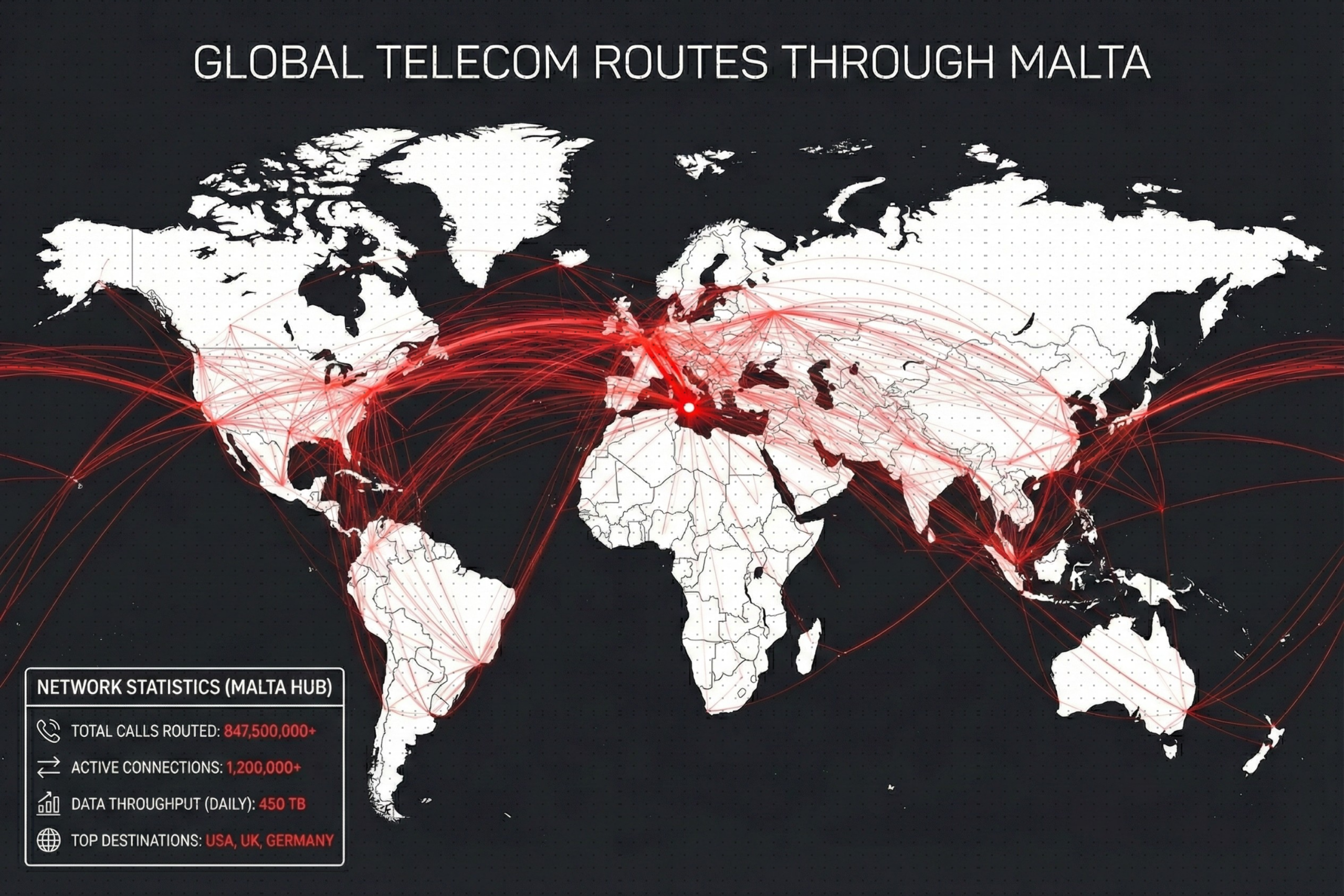
Your network operations center receives an alert at 3 AM: unusual call volume from Nigeria routing through a European interconnect. The CLI is properly formatted, call durations average 90 seconds, and the traffic profile matches a known enterprise customer’s campaign. Do you block it and risk angering a paying client? Or let it through and […]
Verification frameworks authenticate caller identity, but fraudsters have learned to exploit the trust those systems create. This article examines how “verified” calls bypass defenses and what it takes to rebuild trust. According to the Public Interest Network, over a recent 12-month period, phone scams cost Americans an estimated $25.4 billion, affecting more than 56 million […]
In 2025, regulators stopped warning and started acting. Across telecom, companies that once dismissed compliance as a formality began to face real consequences. Fines increased. Investigations expanded. Auditors no longer accepted claims without proof. If your company treats call validation as a technical add-on, it’s time to rethink. Validation is now business protection. It defends […]
Some fraud doesn’t steal identities, it builds them. A few real details mixed with fake ones create a person who doesn’t exist but looks completely legitimate. That’s synthetic identity fraud: convincing, calculated, and built to slip through routine checks. Unlike traditional identity theft, synthetic identities leave no one to sound the alarm. They slip into […]