Don’t Get Trunk-ated: The Case for Gradual TDM-to-IP Migration
It is 2:17 a.m. in the network operations center. Two alarms are live. A legacy TDM interconnect is degrading on one screen while an IP trunk holds steady on another. Fraud flags are spiking at the boundary between them, and nobody wants to be the engineer who called the cutover too early.
This is the daily reality of gradual network migration: the years-long process of transitioning hybrid telecom networks from legacy TDM infrastructure to modern IP systems, one corridor, one route, one partner agreement at a time.
For network operations managers, fraud teams, and finance leads at carriers worldwide, the central challenge is keeping the network secure, compliant, and commercially viable throughout that transition period.
At 1Route, we work with operators navigating exactly this environment. The following is what we have learned about doing it well.
Network Migration Isn’t a Switch: Why Overnight Isn’t an Option
If you have ever sat in a planning meeting where someone suggested a clean, rapid cutover from TDM to IP, you already know how that conversation ends. The room goes quiet, and the engineers exchange looks.
That reaction is earned. TDM infrastructure has underpinned global voice communication for nearly half a century. It is woven into emergency services dependencies, regulatory obligations, interconnect partner agreements, and customer premise equipment that nobody has touched in fifteen years. You cannot schedule a weekend to replace it.
The urgency is compounding for a reason that rarely appears in vendor presentations. The specialized knowledge required to maintain these 1980s-era systems is retiring alongside the engineers who built them. Entire careers worth of configuration knowledge, fault memory, and workaround expertise simply cannot be documented fast enough.
For many operators, a coherent TDM to IP migration strategy is no longer just a technology roadmap. It is a race against a disappearing workforce before institutional knowledge walks out the door permanently.
Parallel Networks Are Expensive, But Chaos is Pricier
Running two networks simultaneously feels like paying twice for the same result. Economically, it is actually the cheaper path.
The Real Cost of Parallel Infrastructure
During transition, operators carry a genuine double burden: TDM maintenance contracts alongside IP scaling costs, two vendor relationships, two monitoring toolchains, and two skill sets on the payroll. For finance teams reviewing monthly infrastructure spend, the line items are hard to defend.
This means capital is committed to infrastructure that is actively being replaced, and operational teams are stretched across environments that demand fundamentally different expertise. That tension rarely resolves cleanly in a budget meeting or a quarterly review.
Why Disruption Costs More
The alternative calculation is more sobering. Service disruption during a rushed cutover triggers customer churn, SLA penalty clauses, and regulatory scrutiny that can follow an operator for years. A single major outage can erase the savings that motivated the accelerated timeline in the first place.
Fraud losses at hybrid network boundaries add another layer of financial exposure that compounds quickly across multiple corridors. Gradual migration spreads risk across a managed timeline. Chaos concentrates it into a single, very expensive moment.
Balancing Dual Infrastructure Costs in Real Time
Let’s go back to the NOC. The team is not debating technology. They are managing what we might call the parallel network operation tax: the monthly accumulation of TDM maintenance, IP scaling, vendor overlap, and staffing costs that arrives reliably alongside every SLA obligation. For many operators, this tax persists for years before the balance tips decisively toward the new infrastructure.
Regulators are beginning to respond. The Digital Networks Act, proposed in January 2026 to replace the 2018 Electronic Communications Code, is specifically designed to simplify the transition to high-capacity networks and reduce exactly this kind of structural drag on operators.
Why Migration Takes Years, Not Months
Migrating a live telecom network is less like upgrading software and more like replacing the foundation of a building while the occupants continue working on every floor above you. One miscalculation and the whole structure feels it.
The 3 to 5 year timeline is not conservative planning. It is an honest accounting of what can go wrong when complexity meets reality. Consider the risk register that any experienced network team carries into a migration:
- Emergency calling obligations that require uninterrupted service across both environments simultaneously, with zero tolerance for gaps
- Interoperability challenges between TDM and IP equipment that manufacturers designed decades apart and never intended to coexist
- Service continuity risk during cutover windows, particularly for enterprise customers running real-time applications
- Regulatory compliance requirements that vary by corridor, country, and interconnect partner, and rarely align on schedule
- Number portability mishaps that strand subscribers mid-transition
- Partner misalignment that stalls entire corridors while contracts are renegotiated
Nobody ever lost their job by going too carefully.

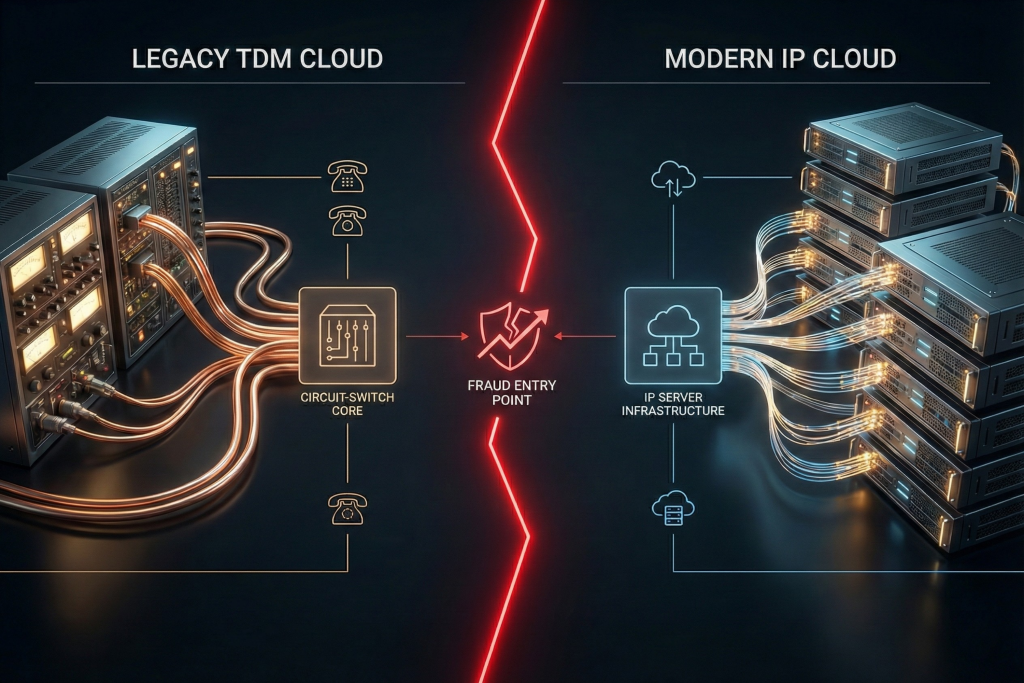
The Seam Where TDM Meets IP Is Where Fraud Lives
Imagine a network where every call arriving from a TDM corridor carries full attestation, every IP trunk is validated in real time, and every boundary between them is cryptographically sealed. Now imagine how far most hybrid networks are from that picture today.
The seam between TDM and IP infrastructure is the most exploited surface in modern telecom fraud. Authentication frameworks like STIR/SHAKEN were designed for IP environments, leaving legacy corridors with inconsistent identity signals and opaque wholesale hops.
Call spoofing risk escalates precisely at these boundaries, where trust semantics differ across segments and traceability weakens. SIM boxing operations further exploit this gap with sophistication, routing fraudulent traffic through the hybrid boundary where coverage is thinnest.
Protecting trust during the hybrid phase requires coordinated defense across every layer of the network simultaneously. This is why 1Route exists as the global standard for trusted voice—and why that defense cannot wait until migration is complete.
The Call That Looks Legitimate Until You Trace It
Back in the NOC, the call flow looks clean on the surface. Trace it one layer deeper and the picture changes completely:
- CLI formatted correctly, origin unverifiable
- Attestation present on the IP leg, absent on the TDM leg
- Wholesale hops with no traceability
- Trust semantics that shift silently at every boundary crossing
Call origin trust is not about how a call appears. It is about whether you can prove where it came from, across every segment of the journey, regardless of which infrastructure carried it.
The bottom line: without end-to-end visibility across hybrid boundaries, legitimate-looking traffic and fraudulent traffic are indistinguishable.
What Security Strategies Make Gradual Migration Viable?
Hybrid networks do not protect themselves. Here is what a security strategy built for the realities of gradual migration actually looks like.
STIR/SHAKEN Is a Foundation, Not a Finish Line
By March 1, 2026, all Robocall Mitigation Database filers must recertify, yet STIR/SHAKEN remains one tool in a broader initiative. It cannot stop spoofing alone without comprehensive analytics behind it. Authentication frameworks verify call identity at the IP layer. They do not see what happens at TDM boundaries, across opaque wholesale hops, or beneath a correctly formatted CLI.
Build a Layered Fraud Prevention Architecture
A reliable call validation strategy follows a simple rule of thumb: validate at every layer you own, and monitor every layer you do not. Network ingress, core signaling, and device endpoints each require independent controls that operate simultaneously rather than sequentially.
Make Analytics Do the Heavy Lifting
Route analytics, anomaly detection, and traceback cooperation convert raw call data into actionable intelligence. Think of them as the difference between a smoke detector and a sprinkler system. One tells you something is wrong. The other actually does something about it.
How to Build a Migration Plan for Finance, Network, and Fraud Teams
Controlled network modernization succeeds when every stakeholder works from the same blueprint.
Says Dácil Jiménez Delgado, Head of Digital Public Policy at Telefónica: “Interdependence and cooperation between different actors are and will be key… to build a common future based on more resilient and advanced digital infrastructures.”
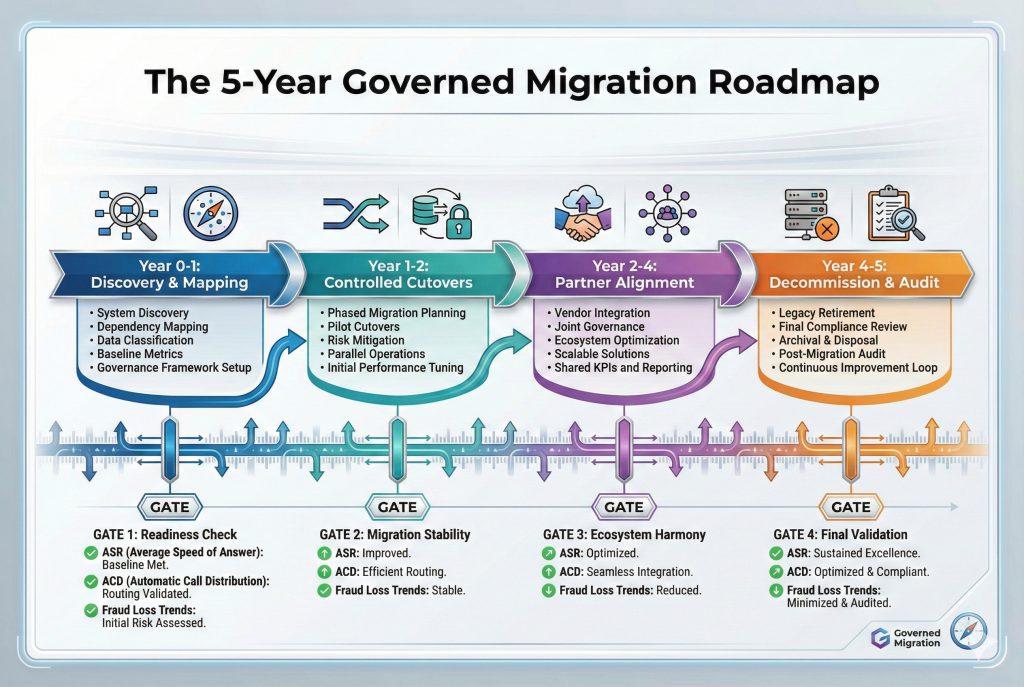
For carriers managing hybrid networks across multiple interconnect partners, that cooperation has to be structural, not aspirational. A workable timeline looks like this:
- Year 0–1 is about discovery: corridor mapping, legacy dependency inventory, and establishing fraud and call quality baselines
- Years 1–2 focus on controlled cutovers, with validation coverage confirmed before any route migrates
- Years 2–4 expand partner alignment and attestation coverage across the network
- Years 4–5 complete TDM decommissioning and establish full auditability
Throughout every phase, track ASR/ACD stability, complaint and dispute rates, fraud loss trends, and traceability completeness. When any metric shows strain, the migration pace adjusts accordingly.
When Gradual Becomes Governance
Before a migration plan has structure, every alarm in the NOC feels like a verdict. Something is wrong, someone is behind, and the network is slipping. With governance in place, those same alarms become instruments on a dashboard—data points in a controlled process rather than signs of failure.
That shift in meaning is what successful controlled network modernization actually delivers. The win condition isn’t a fully IP network on a target date. It’s a transition you can explain, defend, and audit at every stage, with fraud visibility and call trust intact throughout the entire journey.
Gradual is not the obstacle. Ungoverned is.
Ready to see what governed migration looks like in practice? Talk to the 1Route team today.

